You’re here because you want to know about cinecalidad torrent magnet. I get it. You’re looking for a way to access content, and you’ve heard this might be the ticket.
This guide is all about giving you a clear, step-by-step rundown on how these links work and what you need to do to stay safe.
I’ll cut through the technical jargon and focus on the practical steps.
Torrenting is a powerful technology, but without the right knowledge, it can expose you to some serious risks.
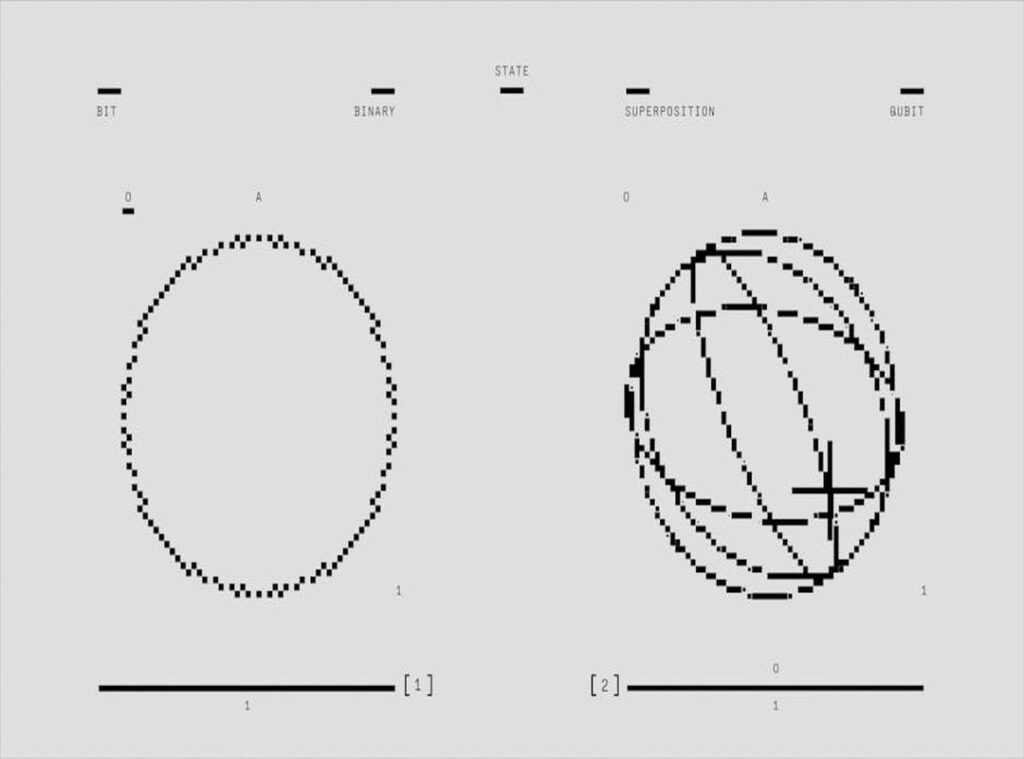
What’s the difference: torrent files vs. Magnet links
A traditional .torrent file is a small data file that acts like a blueprint, pointing a client to a ‘tracker’ server. The tracker coordinates the file sharing between all users, or peers, in the swarm.
Magnet links, on the other hand, are a more modern, serverless alternative. They’re simply a hyperlink containing a unique hash code for the content. This hash code allows a torrent client to find other peers directly through the Distributed Hash Table (DHT) network, without needing a central tracker.
Think of it this way: a .torrent file is like having a party invitation with a specific address. A magnet link is like knowing the party’s secret handshake to find it anywhere.
Sites like cinecalidad torrent magnet prefer magnet links because they offer several benefits. They are more resilient and harder to shut down, making them a reliable choice. Plus, they are easier to share, which means you can get what you need faster and more efficiently.
The top 3 risks you must avoid when torrenting
Torrenting can be a convenient way to access files, but it comes with serious risks. Let’s get into the top three.
First up, IP Address Exposure. When you torrent, your public IP address is visible to everyone sharing the same file. That means anyone can see where you are and potentially target you.
Not a good situation.
Next, Malware and Viruses. Hackers love to bundle malicious software like viruses, ransomware, and spyware with popular downloads. Think about that next time you’re tempted by a free movie or software.
It’s a potential security nightmare.
Then there’s ISP Monitoring and Throttling. Your Internet Service Provider can see all P2P traffic. They might send you copyright infringement notices or even slow down (throttle) your internet connection.
It’s their way of saying, “We know what you’re doing, and we don’t like it.” cinecalidad torrent magnet
Deceptive ads and pop-ups on torrent sites add another layer of risk. These are often gateways to phishing scams or more malware. Stay away from them.
The primary solution to mitigate all these risks? Using a high-quality Virtual Private Network (VPN). A VPN masks your IP address and encrypts your data, making it much harder for anyone to track or infect you.
Remember, when you use cinecalidad torrent magnet or any other torrent, always have a reliable VPN in place. It’s the best way to stay safe and private.
The 4-step checklist for secure p2p file sharing

When it comes to P2P file sharing, security should be your top priority. Always complete these four steps before initiating any download.
Step 1: choose and activate a reputable VPN
A good VPN is your first line of defense. Look for one with a ‘no-logs’ policy and a ‘kill switch’ feature. The kill switch ensures that if the VPN connection drops, your data won’t leak.
It’s a must-have.
Step 2: install a clean torrent client
Go for lightweight, open-source clients like qBittorrent or Transmission. These don’t come bundled with ads or bloatware, which can be a security risk. They’re also user-friendly and reliable.
Step 3: configure your settings for privacy
Enable the kill switch in your VPN settings. For advanced users, bind the torrent client to the VPN’s network interface. This adds an extra layer of protection.
Step 4: verify the link before clicking
Before you click on any cinecalidad torrent magnet link, look for the magnet icon. Also, read the comments on the torrent page. Feedback from other users can give you valuable insights into the file quality and safety.
Pro Tip: Always double-check the source and the feedback. It’s better to be safe than sorry.
By following these steps, you can significantly reduce the risks associated with P2P file sharing. Stay safe out there!
Making smart choices for your digital privacy
Accessing content via cinecalidad torrent magnet links is a technical process that requires a focus on security. Your digital safety depends on the tools you use, not on luck.
Use a reliable VPN, a clean client, and be cautious about what you click. These are the three pillars of safe torrenting.
Respecting copyright laws and being aware of the legal regulations in your specific location is also crucial.
Protect your privacy first. Make sure your VPN is active and correctly configured before you even open your torrent client.
 Quantum Computing & Future Tech Researcher
There is a specific skill involved in explaining something clearly — one that is completely separate from actually knowing the subject. Jesus Stormeraindear has both. They has spent years working with tech maintenance tutorials in a hands-on capacity, and an equal amount of time figuring out how to translate that experience into writing that people with different backgrounds can actually absorb and use.
Jesus tends to approach complex subjects — Tech Maintenance Tutorials, Knowledge Vault, Strike-Driven Quantum Computing being good examples — by starting with what the reader already knows, then building outward from there rather than dropping them in the deep end. It sounds like a small thing. In practice it makes a significant difference in whether someone finishes the article or abandons it halfway through. They is also good at knowing when to stop — a surprisingly underrated skill. Some writers bury useful information under so many caveats and qualifications that the point disappears. Jesus knows where the point is and gets there without too many detours.
The practical effect of all this is that people who read Jesus's work tend to come away actually capable of doing something with it. Not just vaguely informed — actually capable. For a writer working in tech maintenance tutorials, that is probably the best possible outcome, and it's the standard Jesus holds they's own work to.
Quantum Computing & Future Tech Researcher
There is a specific skill involved in explaining something clearly — one that is completely separate from actually knowing the subject. Jesus Stormeraindear has both. They has spent years working with tech maintenance tutorials in a hands-on capacity, and an equal amount of time figuring out how to translate that experience into writing that people with different backgrounds can actually absorb and use.
Jesus tends to approach complex subjects — Tech Maintenance Tutorials, Knowledge Vault, Strike-Driven Quantum Computing being good examples — by starting with what the reader already knows, then building outward from there rather than dropping them in the deep end. It sounds like a small thing. In practice it makes a significant difference in whether someone finishes the article or abandons it halfway through. They is also good at knowing when to stop — a surprisingly underrated skill. Some writers bury useful information under so many caveats and qualifications that the point disappears. Jesus knows where the point is and gets there without too many detours.
The practical effect of all this is that people who read Jesus's work tend to come away actually capable of doing something with it. Not just vaguely informed — actually capable. For a writer working in tech maintenance tutorials, that is probably the best possible outcome, and it's the standard Jesus holds they's own work to.